Pakistani journalist and talk show host Mubasher Lucman learned the hard way that your online information isn’t always as secure as you might think. After hackers gained access to his email account recently, they purged deeper and began sending tweets from his main twitter account (@MubasherLucman).
The hackers went on to set up a Dropbox account, sharing his email files and tweeting the URLs to the world. The files received so much traffic that Dropbox had to disable the links! These leaked emails involve information about an alleged affair along with other secrets.
Lacman has since set up a new Twitter account (@Mubasher_Lucman), but the damage is already done. If anything, this case serves as a model for the type of mess hackers can create for both celebrities and the average citizen.
But he’s not the only one. Pop singer Justin Bieber’s Twitter account was recently hacked, sending a tweet that prompted many of his fans to download a virus without realizing it. Other celebrities like Brittany Spears and Kevin Bacon have fallen victim to online attacks from their Twitter accounts in the past, too, and so have well-established businesses like Fox News and Burger King.
Celebrities are at high-risk of hacks because of their large followings and the opportunity for hackers to do a large amount of damage through exposing secrets, telling lies, or persuading a wide audience under an influential name. Unfortunately, the security measures set in place–such as encrypted data–isn’t always enough to keep hackers away. Instead, users often have to opt into added security measures or increase their privacy settings. For non-techie celebrities looking to tighten their security features on their online accounts and prevent hacks, check out these tips for staying secure online.
Protect Your Email Account and Online Files

Credit: BigStockPhoto.com
When you save important and private documents online—whether for business or for personal use—keeping those files secure can often mean the difference between safety and exposure, identity theft, or blackmail. Tighten up your security to help deter hackers.
Gmail
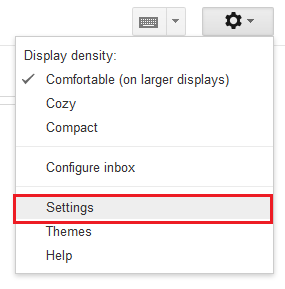
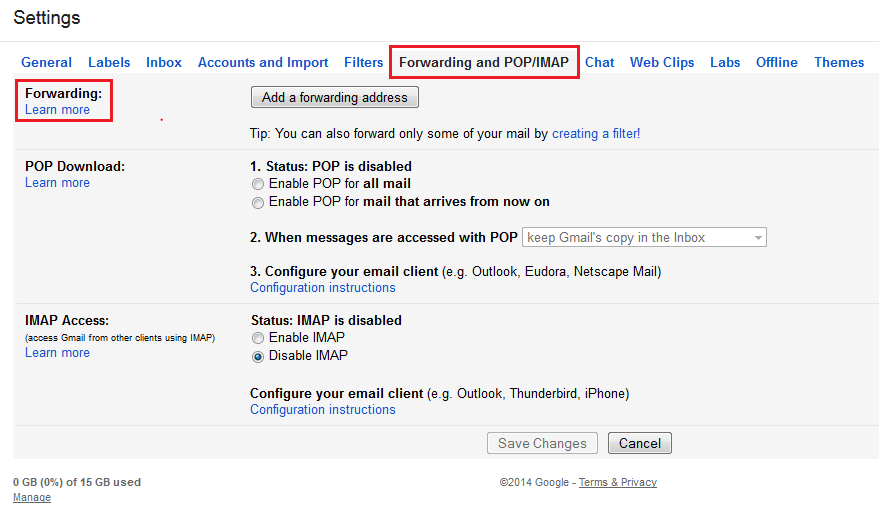
Alone, Gmail comes with many security features and a strong spam filter. When coupled with precautions you take yourself, you can ensure stronger security. After creating a solid password that’s difficult for others to guess, check your “Mail Settings” tab.
In this section, check to make sure your emails aren’t being forwarded and that you’re the only person with access to your account.
It’s also a good idea to add a phone number to your account. This is a more secure, personal means of recovering your password than adding another email or answering a security question. When connecting your phone to your account, you can set it up to receive text messages if someone tries to break into your email.
1. Click on your photo, and then your “Account.”
2. Edit your phone number under your “Personal Info.”
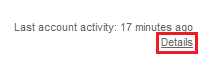
If you suspect unusual activity on your account, Gmail offers a feature that helps you track where you’ve logged in. Simply click on “details” at the bottom of the page, and you’ll receive a list of IP addresses your email was most recently accessed from.
Dropbox
Like Gmail, Dropbox also comes with its own security measures, such as encrypted data. However, you can further protect your account by creating a strong password and enabling a two-step verification login procedure. To do this, click on Name –> Settings –> Security –> Two-Step Verification –> Enable. Follow the instructions to enable the feature.
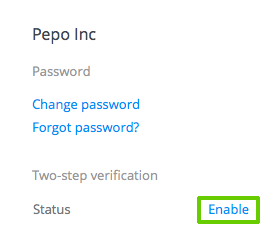
Image via Dropbox
Add an extra level of security by connecting your mobile phone to the account to receive text messages. This creates a login process where a security code is sent to your phone when you login. To enable this, enter your phone number when setting up the two-step verification.
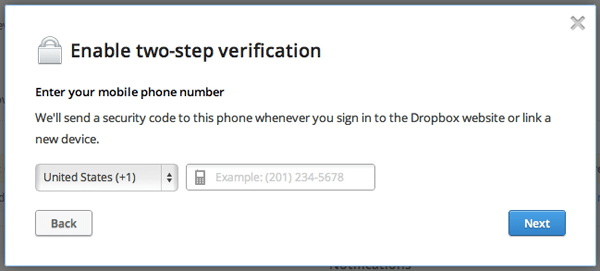
Image via Dropbox
Since files are available to anyone who has the link, it’s also important that you’re conscious of who you’re sharing folders with. If you don’t want to share your folders, make sure they’re set as “normal” folders and not as “shared” folders. If you’ve made a mistake, you can unshare folders by going to “options” in the sharing tab and clicking “unshare folder.”
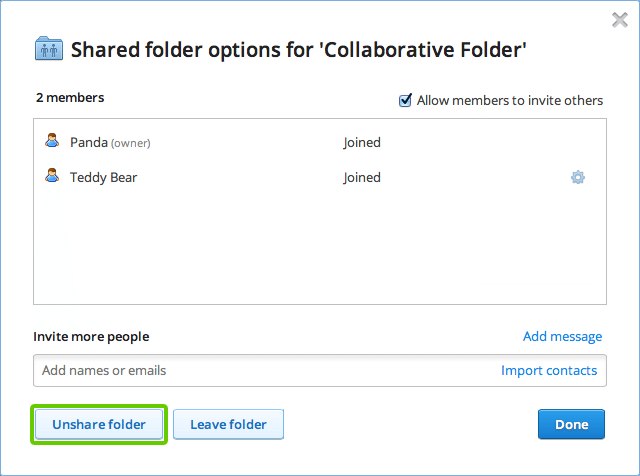
Image via Dropbox
WordPress
WordPress is a common blogging platform used by celebrities and others alike, which can make it a large target for hackers who want to access celebrity accounts and expose secrets to a wide audience through blogging.
Start by choosing a secure server. Consider staying away from shared servers. While hosting on a shared server is a practical option for people who can’t afford their own VPS, a more secure server is worth it for public figures who are serious about maintaining their image. Not sure if your host is as secure as others? Check out these secure WordPress tips.
Another way to protect your account from brute force attacks is to create a new user and get rid of the “admin” username. You can set up a different username during the registration process. Make sure to create a password that’s tough to guess with a combination of capital letters, lower case letters, numbers, and symbols. These techniques will keep people from guessing your login information. For added security, install a plugin like Limit Login Attempts that prevents people from logging in after a certain number of tries.
When installing plugins, check that they’re up-to-date so that you get the most secure options available. Update new versions of WordPress, too. You’ll receive notifications when these updates are available, so simply click on the update link.
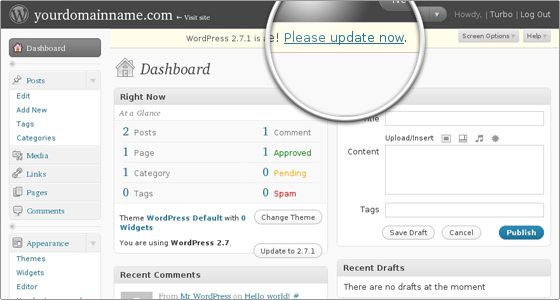
Image via Siteground
Keep Your Social Media Accounts Secure
Social media accounts are a prime target for hackers because they can cause so much damage and get ahold of heaps of private information. In fact, over 600,000 Facebook accounts are hacked daily. Basic social media security tactics involve:
- Changing your passwords frequently (and storing them in a secure location if you have to write them down)
- Accessing social media accounts through a third-party social media platform like Hootsuite that will warn you of malicious links
- Limiting access to your accounts so untrustworthy employees can’t hack in
Understanding specific actions you can take on each platform, however, can further boost security. Use these social network specific tips for each account.

Credit: BigStockPhoto.com
Facebook’s convenient security tools allow you to test how others see your profile and posts. When on your private profile, click “View As…” in your cover photo section.
This will allow you to see your profile as the public sees it. At the top, you can also click “View as Specific Person” and type in a friend’s name to see what he/she sees.
To ensure your posts are kept from your public profile, click on the far right drop-down menu at the top.
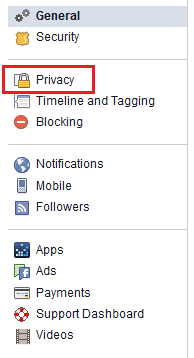
Click on “Settings,” and then “Privacy.”
Here you can change who sees your future posts as well as edit who can contact you and who can view your personal information that you provide on your profile, such as your email and phone number.
In the “Settings” section, you can also click on “Security” on the left menu. Here you can add additional security measures–such as receiving text messages when someone tries to access your account–set up text message security code confirmations, and even view when and where you’ve logged in recently.
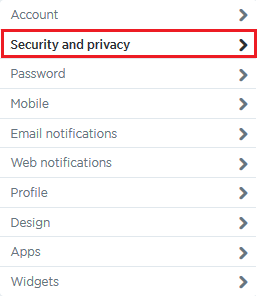
Like Facebook, Twitter offers an array of safety features. Start by clicking the gear icon on the top right-hand side of the page. On the drop-down menu, click “Settings.”
On the left-hand menu on the “Settings” page, choose “Security and Privacy.”
Use the options on this page to increase your security. Set up login verification to deter brute force attacks, require personal information when asking to reset your password, and add privacy to your Tweets.
Since many businesses allow multiple people to access their Twitter account and some celebrities may have assistants who manage their personal account, it’s important that you only give out login information to trusted individuals. Employees have been known to hack their employers’ accounts and cause irreversible damage to their personal and their company image.
When you login to Twitter, make sure that you’re on the correct page, too. If you see something other than https://twitter.com/login in the address bar, you could be handing your login information over to someone who’s running a phishing scam.
With Twitter, shortened URLs are also a huge concern since you can’t tell where they’re leading you. To avoid heading to a dangerous site or downloading a virus, use a URL expanding tool to check where the link is taking you.
Google+
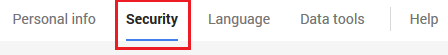
Google+ features many settings that help you maintain a secure account while keeping hackers from accessing it. Since all parts of Google are connected to one account, you can maintain the same security measures as you have with your Gmail account. Start by setting up the two-step verification login process.
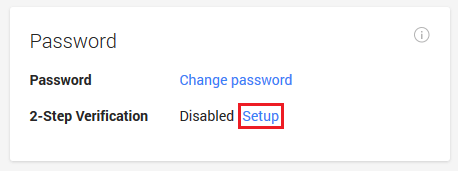
1. Go to your “Account.”
2. Click on “Security” in the menu bar at the top.
3. Click “Setup” under “Password” and “2-Step Verification.”
In the same security section, you can also set up a recovery phone number and view recent security-related issues on your account.
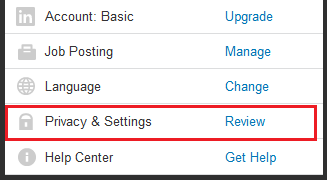
To access your LinkedIn settings, hover over your profile picture at the top right-hand side of the page. In the drop-down menu, click “Privacy & Settings.”
Under the “Profile,” “Group, Companies, and Applications,” and “Account” tabs on the left menu, you will see “Privacy Controls” to manage each option. Use these options under “Privacy Controls” to tighten your account privacy settings.
Once you’ve organized those settings, go to your “Account” tab. Under “Settings,” you’ll find a link titled “Manage Security Settings.”
It’s here where you can enable a secure connection when browsing LinkedIn (although some LinkedIn applications will not be available). You can also set up your two-step verification process to keep your account more secure when logging in. LinkedIn uses text messages for their two-step login, so you will have to enter your phone number.
Prevent Hackers From Accessing Information on Your Mobile Device
Taking the above precautions often isn’t enough to completely protect your information. If someone gets ahold of your information from your mobile device—whether by stealing the device or by hacking into it—they can easily access the accounts you’re already logged into.
Start by avoiding public Wi-Fi networks. Since you’re connecting to a shared network, it’s easier for hackers who are also on the network to access your information. Instead, connect to the Internet via your own VPN. Continue securing your mobile device through these platform-specific tips and security apps.
iOS
When using an iOS device, start by disabling your automatic Wi-Fi capabilities. With this enabled, your device will automatically search for open Wi-Fi networks and connect to them without your knowledge, leaving you vulnerable to attacks. If you’ve connected to public networks in the past, you likely have this information saved on your device, and it will connect the next time you’re around that network. To disable this option, head to your network settings and turn off “Auto Join” or forget the network.

Image via Apple
To add a level of security to your Apple device, set up a password. Go to your general settings, click on “Passcode Lock,” and set up a 4-digit PIN.

Image via TheFullSignal
Android
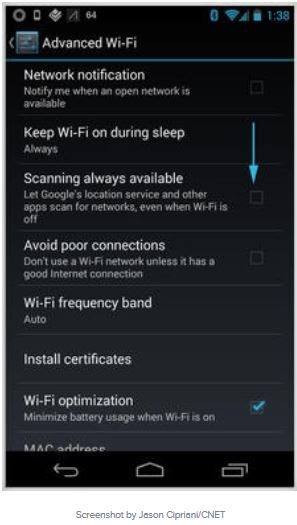
On Android, you can disable your automatic Wi-Fi settings by launching your Wi-Fi setting options. Head to “Advanced Settings,” and uncheck the “Scanning Always Available Box.”
Set up a password by going to Settings –> Location & Security –> Screen Unlock –> Set Up Screen Lock. Here you can choose from one of three password types: Pattern, Pin, or Password. Choose and verify your choice.
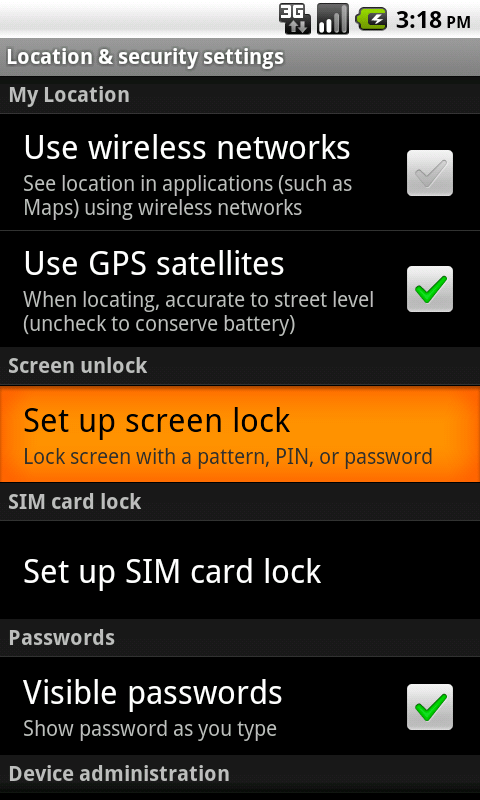
Image via csuchico.edu
While each version of Android varies, you should be able to reach the settings much the same way on each.
Safety Apps
Along with these tips, you can install additional apps to add even more security to your mobile device. With Norton Mobile Security, for example, you can lock and wipe your phone remotely if it’s been stolen. This app also features anti-virus and malware protection. There’s also the free Avast! for Android, which scans for viruses, allows you to remotely lock your phone, and locates your phone if you’ve lost it. On Apple products, you can grab Find My iPhone to track lost devices or VirusBarrier that scans files when you want it to, such as when downloading email attachments.
When downloading apps, be sure to check the app’s privacy settings. If the app is requesting information on your location, passwords, and access to your text messages, it’s smart to deny access.
Recap–Safety Tips:
- Never connect to public Wi-Fi
- Scan your computer and devices for viruses regularly
- Change passwords periodically
- Store passwords in a safe location (not on a post-it note on your desk!)
- Choose the most secure password option, such as two-step verification
- Download anti-virus and other safety software
- Always check links and attachments to prevent downloading a virus








Kaloyan Banev
03/06/2014 at 9:09 am
Good tips that everybody should follow. Unfortunately I think that most people read that kind of articles when it is already too late and security is already compromised.