A software engineer, Rob Heaton has recently made public his discovery of a vulnerability in the messaging platform, WhatsApp. According to Rob, the latest WhatsApp vulnerability can allow anyone to discover who is talking to whom.
The stalker can find out by using just four lines of JavaScript code. Anyone with an intent can discover exactly when two people are talking to each other at WhatsApp through correlating the data and personal information.
Also Read: Beware WhatsApp users – new phishing scam in guise of background color options
In his blog post, Rob stated:
“You’re dying to know whether your friends Lara and Tara are secretly dating. You can’t help but write multi-variate cross-correlation software that shows a striking alignment between their WhatsApp usage patterns”
New post showing how to track an unsuspecting target's sleep pattern (+more) using only their phone number+WhatsApp. https://t.co/4huvTP4sBg
— Robert Heaton (@RobJHeaton) October 9, 2017
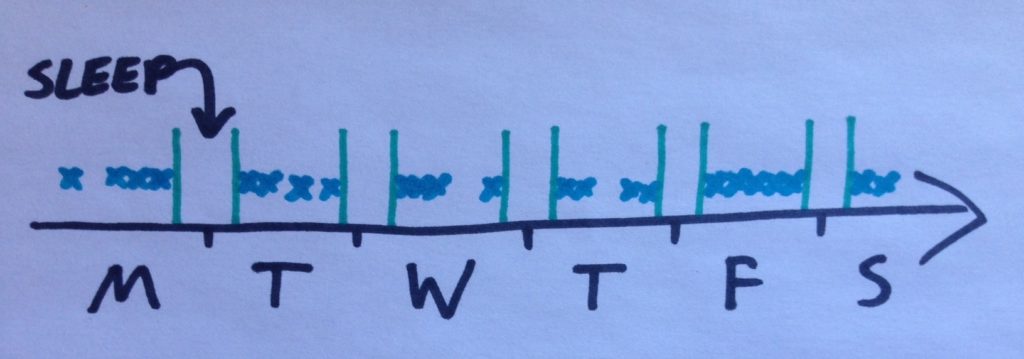
Rob began his blog post by crafting a scenario in which a friend was trying to discover the sleeping pattern of a contact, named Steve. In the scenario, he wanted the stalker to find out whether Steve was getting 8.5 hours of sleep during the night to prepare for a charity walk. Rob said:
“The plan is simple. Every 10 seconds, you check your target’s WhatsApp status, and note if they are online or not”
Steve’s ‘last seen’ time on WhatsApp and the times he came online on the app was noted down by the stalker. Thereafter, he interrelated the data and revealed that Steve did not sleep as much as he was ordered to.
Somehow Rob Heaton succeeded in going through the WhatsApp vulnerability by penning a short Chrome extension. He wrote:
“You set your Chrome extension running and hide the laptop under your bed. You come back a week later and see what Steve Steveington has been up to. Later, you copy and paste the output from the developer console and draw a couple of graphs”
The graph of the stalker would somehow be apparent in the following manner:
It is significant to state that interlinking the outlines of two or more persons requires a longer code. However, the very same method would be applied.
Facebook Messenger found out the same vulnerability
Facebook Messenger also notifies the other users when a specific user has been online, offline or idle. Subsequently, it also went through the same flaw last year. The vulnerability on Messenger also empowers the stalkers to chart when their friends are actually awake or asleep.
Quick Read: Phew! Users can now delete sent messages on WhatsApp
On Monday, Rob wrote in his blog post:
“Monitoring Steve Steveington on WhatsApp presents a different set of challenges to monitoring him on Facebook”
He further added:
“Facebook sends data to your browser using straightforward HTTP requests that you can easily write a program to mimic. However, WhatsApp communicates with your browser using a much more complex Web Sockets-based protocol”
WhatsApp has not yet commented about the vulnerability made public.